
Digital Damocles
Back to /blog/newsby
Georg C. F. Greve

Mon Mar 18 2019
As a child, I’ve been fascinated by the tales of the ancient Greeks. Not realising it at the time, this may very well be where my interest in computer security was sparked. A surprising number of principles for good security can be explained using imagery from a civilisation thousands of years ago, long before the invention of the computer. Why is that? Security is always human. And humans are not evolving as fast as our technologies. So we keep making the same mistakes ever since a huge wooden horse was dragged inside the city walls of Troy.
One of these tales is that of Damocles. Intoxicated by convenience, wealth and power, he was oblivious to how fragile they can be until he found himself dining under a huge sword held only by a single horse’s hair. In much the same way most people today are blissfully unaware how fragile their digital lives are. We have hundreds of accounts with web sites, services and apps. Each of these accounts represent a part of us. They are representations of our real identity. The one thing holding it all together? Our e-mail inbox.
Once in control of your e-mail inbox, even weak attackers can successfully take over your life by initiating password reset procedures with the sites and services they are interested in. Common security measures used by most people are useless against this kind of attack. Which is why phishing sites offer wonderful, shiny, free things with the sole purpose of getting your email address. E-mail is the worlds’ largest unverified identity infrastructure, and it is poorly prepared to handle the central role we are giving it.
Fundamentally, the issue is one of lack of verified identity. An e-mail inbox is only a conduit for information. That conduit may end up with the person you think it does. Or someone else. There is currently no solution to make sure the information ends up with the right people. Just like you do not know the email was really sent by the person you are thinking of. To make it worse, education alone cannot solve this issue. Even educated people and technologists fall for phishing mail. Because all too often the e-mail account used was real. And that is everything legacy e-mail allows you to verify.
Verified identity is the missing link to move from inboxes to people. Adding verified identity to e-mail protects the reputation and social network of the sender. It makes the sender far more trustworthy to the recipient — allowing the recipient to separate truth from scare. For verified identity to truly make this possible, it must however meet certain minimum requirements. These are often summarised under the heading of “self-sovereign identity.”
The very executive version is: such an identity must be secure, persistent, under control of the user and its data has to be protected and scarce. Also, it must be portable and interoperable, and meet certain technical requirements, such as being implemented in Open Source Software to allow for verification, improvement and implementation in systems of multiple vendors. But I would argue that the above definition is critically incomplete.
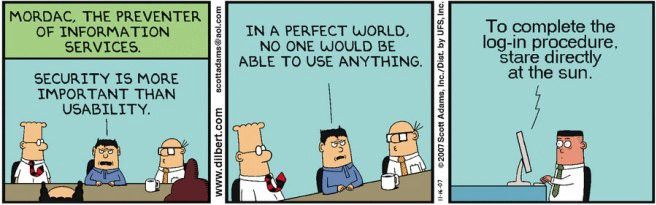
Security and usability are often falsely treated as adversaries. Convenience and usability are perhaps the most important ingredients to make this work. Any such verified identity should be invisible, like magic. It should just work and feel natural to the user. It should be fun, and not a burden to use. Its adoption should happen where the users already are, with no migration or change of habits required.
Verified identities for email — and anything else — hold the promise of changing the underlying dynamic of interaction and business. Instead of wallet to wallet or account to account, the interaction pattern becomes person to person. Combined with technologies like blockchain and the application of “Zero Knowledge Proof” for protection of privacy, the result would truly be a more humane world. One that is not inbox-to-inbox, but person-to-person.
That is what Vereign is working towards. Our solution delivers the technology for a platform of trust that is run by a number of organisations and puts verified identity in the hands of the people. It also uses smart contracts to incentivise higher levels of trust and verification, offering credits as a basis for equitable exchange between people and organisations.
We have already managed to build this into the world’s largest e-mail provider (Gmail) and the most open and most popular webmail solution (Roundcube) as well as LibreOffice Online. Sign up for our prototype, join us in our community and become part of the journey.